Mobile Measurement Partners (MMPs) have long been the industry’s first line of defence against mobile ad fraud. Through SDK integrations and last-click attribution, they have helped brands track installs and flag suspicious activity based on known patterns such as:
- unusual install spikes
- abnormal click-to-install times
- repetitive device IDs
While this works well for obvious fraud, the challenge today is far more sophisticated.
Fraudsters now mimic normal user behaviour, making fraudulent traffic look genuine. In many cases, they have effectively reverse-engineered MMP detection logic and learned how to stay within acceptable thresholds.
By carefully blending different traffic types in calculated proportions, bad actors are able to pass MMP checks and continue draining campaign budgets unnoticed.
This is why the common concern today is clear: MMPs catch obvious fraud but often miss blended fraud.
In this blog, we cover:
- why MMPs struggle to catch blended traffic
- how mixed traffic gets a green signal in campaigns
- how brands can protect themselves beyond basic MMP checks
Why MMPs Struggle to Catch Blended Traffic
MMPs are designed to detect fraud using known red flags such as unusual click-to-install times, or repetitive user behavior.
But today’s fraudsters have become smarter. Instead of sending clearly fake traffic, they mix fraudulent activity with genuine users so that nothing looks suspicious at first glance. This makes the traffic appear legitimate on the MMP dashboard, while budgets continue to get quietly drained in the background.
Bot Traffic – Hiding Behind Volume
Bots generate large volumes of clicks and fake installs, creating an illusion of strong campaign activity. When this fake traffic is mixed with real users, the overall data starts to look normal. Click and install ratios are high where one click is followed by one install hence time patterns seem balanced, device IDs appear varied, and nothing stands out as an obvious anomaly.
Because MMPs are typically built to detect extreme outliers, this blended fraud often slips through unnoticed.
Last-Click Attribution – Stealing Credit for Real Installs
In fraud tactics like click spamming and click injection, fraudsters either flood the system with fake clicks or place a click just before a real user completes an install. This helps them hijack last-click attribution and steal credit for a conversion that should go to a genuine source.
Since the install itself is real, the MMP often treats it as genuine. The fraud happens at the click stage, which many surface-level detection models fail to catch effectively.
Incentivised Traffic – Real People, Misleading Results
This is one of the hardest forms of fraud to detect because it involves real people. Users are paid or rewarded to install an app, so all the signals look human; real IP addresses, normal device behavior and natural session activity.
To an MMP, this traffic appears completely clean. The problem usually becomes visible only later, when retention and engagement suddenly drop after the campaign budget has already been spent.
Read in detail about device fraud
How the Data Exposes the Evasion, MMPs Cannot Detect
The data below highlights findings from a campaign ran between Sept–Oct 2025, where bot traffic was mixed with organic installs, making it difficult for MMPs to separate real activity from fraudulent traffic. Here’s what the data shows:
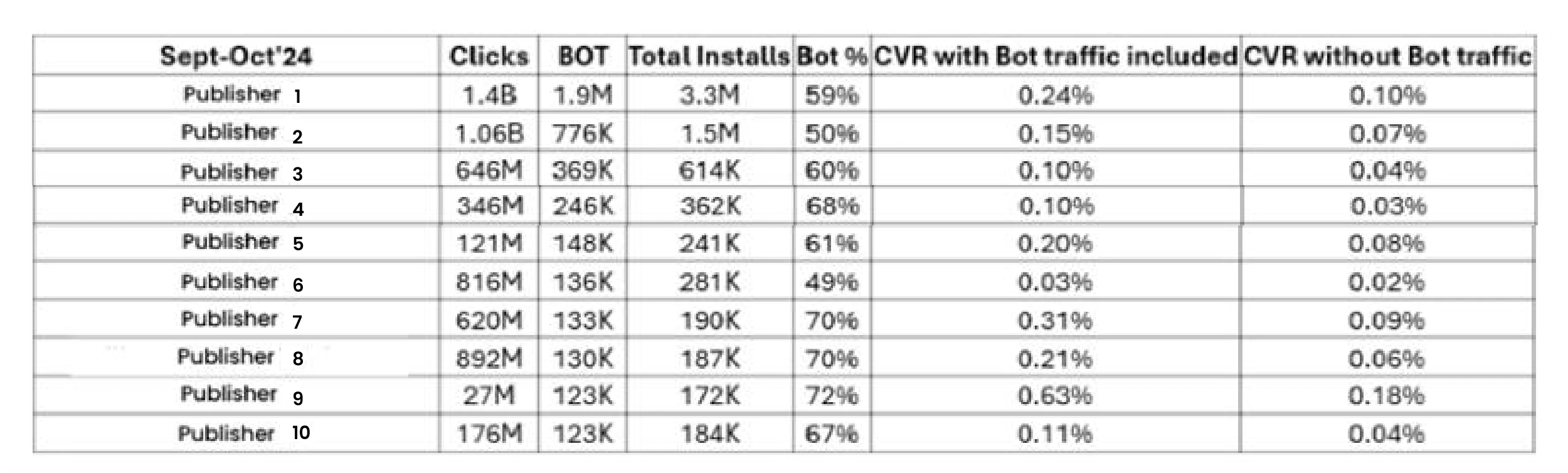
- The conversion rate gap is the clearest proof of hidden invalid traffic: The top source, publisher 1, shows conversion rate falling from 0.24% to 0.10% after bot traffic is removed, meaning nearly 58% of the apparent performance was artificial uplift.
- Massive click volume is creating a false sense of scale: Publisher 8 delivered 816M clicks, but its clean CVR drops to just 0.02%, huge activity on paper, but almost no genuine conversion value.
- Strong reported CVR can still hide severe bot contamination: Publisher 11 appears to be a top-performing source with 0.63% reported CVR, but once bots are removed it drops to 0.18%, with 72% bot share, indicating invalid traffic driving the most performance.
- Bot-heavy traffic is not an outlier – it is widespread: 7 out of 10 visible publishers show bot share above 60%, including sources like publisher 5 (68%), publisher 9 (70%), and publisher 10 (70%), despite all of them marked as clean by MMP.
- Even mid-volume sources show inflated performance: Publisher 7 drops from 0.20% to 0.08% CVR, while 61% of its traffic is bot, showing that inflation is not limited to only the largest traffic sources.
The most dangerous fraud isn’t what MMPs catch, it’s what they don’t. Understanding the evasion tactics is the first step to building detection that actually keeps up.
How Brands Can Protect Themselves from Mixed Traffic Beyond Basic MMP Checks
MMPs should be treated as the first layer, not the only layer. An independent layer of validation through mobile ad fraud solution like mFilterIt’s empowers brands against mixed traffic, catching sophisticated tactics that MMPs miss –
- Recover stolen conversions through full click-path validation: Move beyond last-click attribution to validate the complete user journey from first touch to install so click hijacking and attribution theft are identified before they drain budgets.
- Pinpoint fraud sources with publisher-level transparency: Gain granular visibility down to publisher, sub-publisher, placement, and traffic source level to isolate hidden fraud pockets and eliminate waste at the source.
- Improve acquisition quality by validating real user intent: Go beyond app install counts and measure retention, session depth, registrations, and purchase signals to separate genuine users from low-intent or incentivised traffic.
- Surface blended fraud early with CVR and traffic anomaly detection: Monitor conversion gaps, abnormal click bursts, and sudden traffic mix shifts to detect bot-driven or manipulated traffic before it impacts performance metrics.
Conclusion
Blended fraud is changing the way brands need to think about campaign validation. What once appeared as a reliable defence layer is now being challenged by fraud tactics that are far more calculated and harder to spot.
This makes it critical for brands to look beyond standard MMP signals and adopt deeper monitoring frameworks like mFilterIt’s Valid8 that can uncover hidden manipulation across clicks, installs, and post-install behaviour.
In a high-investment digital ecosystem, protecting media spends is no longer just about catching obvious fraud, it is about identifying the traffic that is intentionally built to look real.
FAQs
How do fraudsters bypass MMP detection?
They mix fake traffic with real user activity, making fraud look genuine and harder for MMPs to detect.
Why do MMPs miss blended fraud?
Because blended fraud mimics normal user behaviour and stays within acceptable detection thresholds.
What are click injection and click spamming?
These are fraud tactics that use fake clicks to steal credit for genuine app installs.
How can brands detect fraud beyond MMPs?
By using click-path validation, publisher-level insights, and post-install quality checks.
How can brands protect campaigns from mixed traffic?
Treat MMPs as the first layer and add advanced fraud monitoring for deeper validation.



