Bot traffic is taking up more than half of the internet traffic. Out of which, 37% of the traffic is driven by bad bots. (Source: Imperva)
And this bot traffic is beyond just inflated activity.
Sophisticated ad fraud techniques penetrate the funnel, impacting not just analytics but end goals like sign-up, purchase, etc.
They can bypass basic ad fraud detection methods easily, mimicking human-like behaviour. It skews the data, further impacting decision-making, conversion rates, and retention across mobile and web campaigns.
That is why it is important for advertisers to know about not just surface-level signs of ad fraud but also the sophisticated indicators.
In this article, we’ll break down some of the signs of ad fraud that we have observed in the campaign analyzed. Let’s dig in.
What Differentiates Sophisticated Ad Fraud Techniques from Basic Bot Traffic?
Basic bot traffic is easier to detect. It often creates visible spikes like traffic coming from locations outside the targeted region, same devices, unrealistic click volumes, or abnormal engagement patterns.
On the other hand, sophisticated ad fraud is different. Instead of obvious anomalies, it mimics human-like behaviour. The manipulation happens inside patterns that are harder to identify and detect: OS distributions, CTIT inconsistencies, imperceptible ad placements, IP clustering, or traffic coming from incent fraud.
Basic bots inflate numbers. Sophisticated fraud impacts performance intelligence. That is what makes it more dangerous.
It does not just waste budget. It influences optimization decisions, attribution models, and scaling strategies, without triggering immediate suspicion. Therefore, understanding this difference is the first step toward detecting it.
Now, let’s have a look at some of the sophisticated ad fraud signals.
Sign 1: Heavy install coming from older Android OS versions
Fraudulent affiliates using bots and emulators running on older Android OS versions to generate fake app installs.
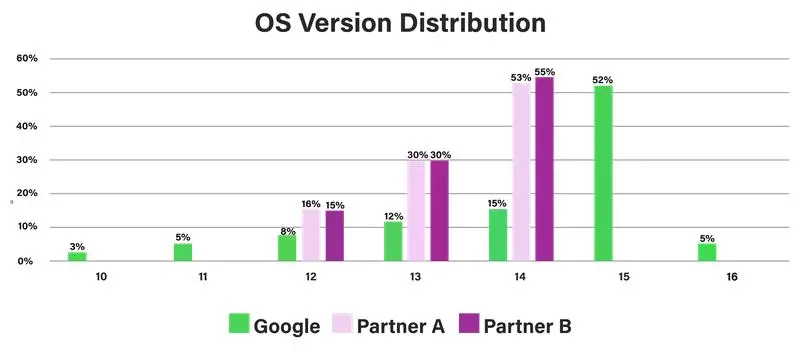
After comparing OS version install distribution across different traffic sources:
Google installs were spread across multiple OS versions (10-16), reflecting a healthy and natural user base. However, two affiliate partner sources revealed a very different pattern.
- Partner A and Partner B showed a heavy concentration of installs on OS 12, 13, and 14
- While the benchmark (Google) traffic was distributed more broadly across OS 10–16
The mismatch clearly indicated emulator-based or bot-driven installs.
Sign 2: Google Play installs happened before the user clicked on an ad
Click-to-install time (CTIT) measures how long it took a user to install an app after clicking on an ad.
Naturally, an app install takes up to minimum 20-30 seconds. However, in one of the campaigns we noticed app installs taking place even before the users clicked on an ad, resulting in negative CTIT. This is a clear indicator of mobile ad fraud.
Therefore, extremely short or negative click-to-install time indicates click injection.
Sign 3: Inflated Installs Coming From Incent App
In one of the campaigns, we observed that a telecom provider was unknowingly running ads on an incent app.
Users were redirected through a shared link, asked to install the app, and complete specific steps to earn rewards. This resulted in a high number of installs, but the actual engagement remained low.
The majority of users completed the required action only to earn coins and did not return. This clearly indicated incentive-driven traffic rather than genuine user acquisition.
Sign 4: Invalid Traffic Coming From Imperceptible Window
In one of the web campaigns, 99% of traffic was coming from an imperceptible window (also known as pixel stuffing ) through a specific publisher source.
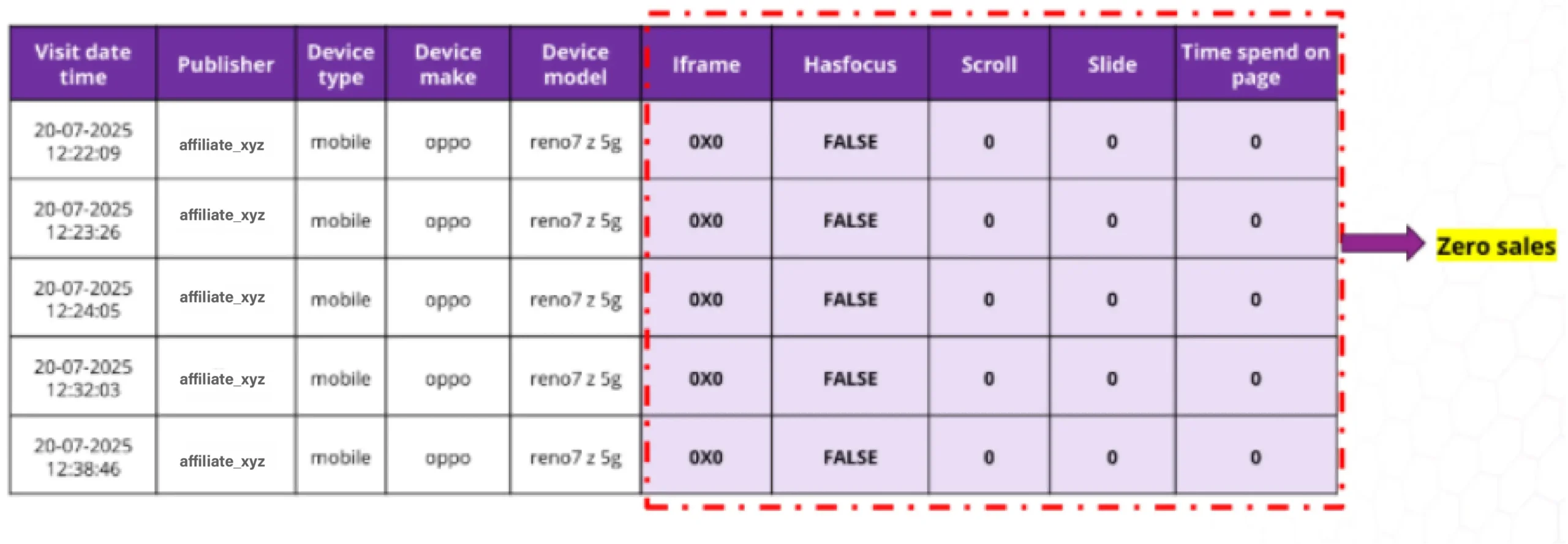
This means the ad was technically loaded in 0x0 iFrames, but not actually visible to users.
Although impressions and traffic volumes appeared normal, user engagement metrics clearly indicated non-human behavior. Analysis revealed:
- Repetitive browser agent across sessions
- Over 70% of data originating from a single IP cluster
- Zero scroll activity and no sales generated
This means advertisers must check not just if the ad was delivered but also if the ad was actually viewable.
We have broken down how to move beyond the viewability myth. Check it out here.
Sign 5: Repeated Ip Traffic From The Same Subnet (Invalid Traffic Pattern)
In genuine campaigns, IP addresses are typically distributed across diverse networks. But what we observed was different.
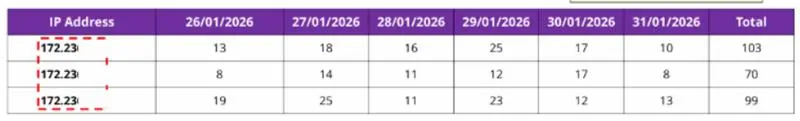
At first, the traffic appeared strong. But on deeper evaluation of IP-level data, we found that a large portion of clicks and visits were traced back to a single IP subnet.
Each IP was generating more than 70+ clicks, consistently inflating traffic. The concentration of activity within a contiguous subnet suggested coordinated or automated behavior rather than random user traffic.
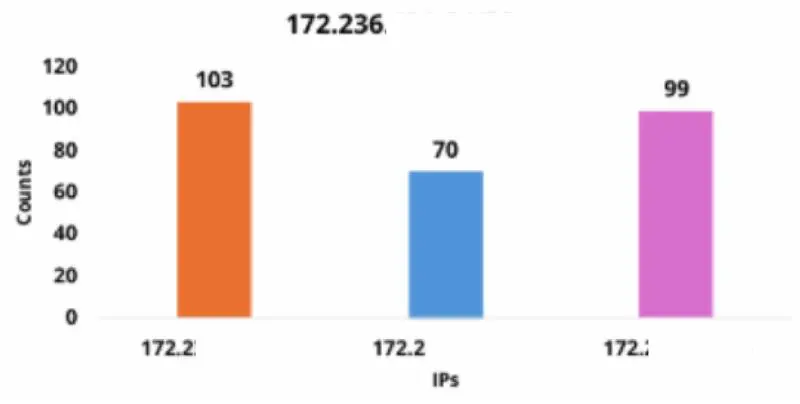
If a significant share of your traffic is coming from closely grouped IP ranges. especially those flagged under VPN or proxy networks, it requires immediate audit.
Volume alone does not indicate performance. Source diversity does.
How Can Advertisers Identify Sophisticated Bot Traffic?
Detecting sophisticated ad fraud requires moving beyond surface-level indicators. Here are key actions advertisers should take:
Analyze Deeper Behavioral Patterns
Validating only surface-level signals like clicks and installs is not enough. You need to monitor click-to-install timing distributions, engagement depth beyond first interaction, repeat device and IP behaviour, etc. These patterns uncover anomalies that standard filters miss.
Benchmark Across Trusted Sources
Compare partner traffic against known clean channels, ecosystem adoption trends, and natural engagement ranges. Discrepancies from benchmarks often reveal non-genuine or invalid traffic behaviour.
Validate Before Scaling Budgets
Campaign scaling should never happen without ad traffic validation. High volume doesn’t mean high value. Invest in tools that provide real-time ad fraud detection, cross-source transparency and analysis, alerts for sophisticated patterns with proofs and in-depth understanding of new emerging patterns as well.
At mFilterIt, our ad fraud detection tool – Valid8, helps detect ad fraud signals that ad platforms and MMPs often overlook. They also allow you to:
- Understand true user intent
- Exclude invalid traffic before optimization
- Improve confidence in performance decisions
So, if your installs are rising but revenue isn’t, if traffic is scaling but retention is weak, it’s not an optimization issue. It’s a traffic quality issue. Therefore, validate what’s driving your campaigns.
Connect with our experts to know how we can help.